Securing the Digital Financial Ecosystem Abroad

The 8th annual MITRE embedded capture the flag (eCTF) competition is underway and this year, we have more competitors than ever. Based on the success of the program, we have opened this year’s competition up to cyber and embedded systems company sponsors creating even more opportunities for participating students. To better understand the impact of the program, we met with five former eCTF participants who earned prominent positions in cyber engineering at MITRE. Their experiences with the eCTF competition as a springboard for their careers are inspiring.
Many participants join in the competition multiple times; the challenge uses different scenarios each year (see all the different challenge over the years). According to Patrick O’Leary, a software engineer at MITRE, one of the most satisfying aspects of participating in the eCTF was building software in a way that that offered experience and a taste of what it’s like to build software as a professional software developer on a team.
Real world training for college credit
“A lot of the skills and mindsets that you adopt during the eCTF aren’t taught in school,” emphasizes Jake Grycel, now an embedded security engineer at MITRE. “Some schools have cybersecurity courses, a few may have embedded security courses,” he grants, “but for the eCTF players have to engage those concepts and get another level of understanding.”
The eCTF is unique in that it challenges students to create systems that stand up to other attacks as well as implement attacks on other designs: “I came in not being in embedded or in security and I came out an embedded security engineer. This is a great opportunity to get your hands dirty on the kind of stuff you’d be doing in the real world. It is a closer experience to the real world than anything else that I’ve done in my entire time at school,” declares Ben Janis, now senior embedded security engineer and heavily involved eCTF organizer. Plus, many colleges are open to granting credit hours for their experience!
Adversaries are only human
AFCEA 40 Under 40 Winner and former participant Maretta Morovitz-Orta affirms that the most useful part of the competition was how it helped her see adversaries as human beings. She points out that in the eCTF you get to engage in both defensive and offensive tasks, so teams initially learn what parts of the challenge are difficult to create and then can use this key information during the attacking phase. This is because other teams are likely to have had the same experience, making it a potential weakness. She remains aware of the human behaviors of adversaries conducting intrusions or malicious behavior in her position at MITRE, which focuses on adversary engagement, malware analysis, and reverse engineering.
Indeed, the eCTF has been vital for a lot of the work that Maretta does at MITRE, looking at threat informed defense, adversary engagement, and cyber deception. She’s also a founding member of MITRE’s Cyber Deterrence and Adversary Management team and all these different topics really revolve around this concept of seeing the adversary as a human being and not just as an indicator or an IP address or a piece of malware.
Been there, done that
Yes, you must remember that adversaries are human beings and below we have more advice that comes from participants and will aid future competitors:
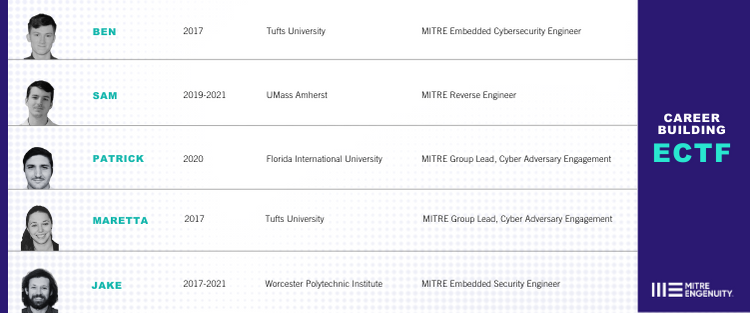
Where are they now?
Participation in the eCTF led to enhanced career prospects for each former participant. Keep reading to see when each person competed, through which school, and what their current job is at MITRE!
Your turn
These eCTF participants found that their experiences propelled them into an exciting career in embedded security. Contact ectf@mitre.org if you’re interested in a fun way to gain training that enables you to transition into one of the most in-demand careers right after college!
Check out our full ECTF discussion with Ben, Maretta, Sam, Jake, and Patrick below!